The Restorepoint user interface pages share some common features. These features include:
- A menu bar at the top of the page, for navigating between the different functions
- The username of the logged in user at the top right-hand side of the screen
- A footer that displays the current software version, serial number, license expiry, and time
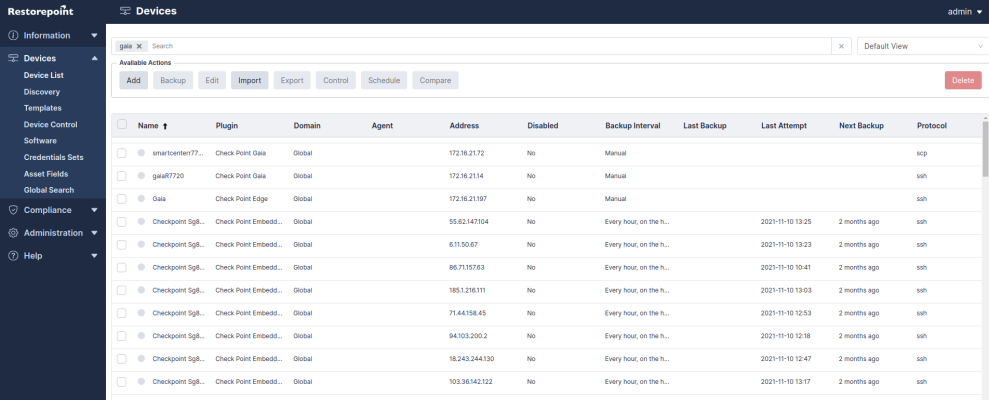
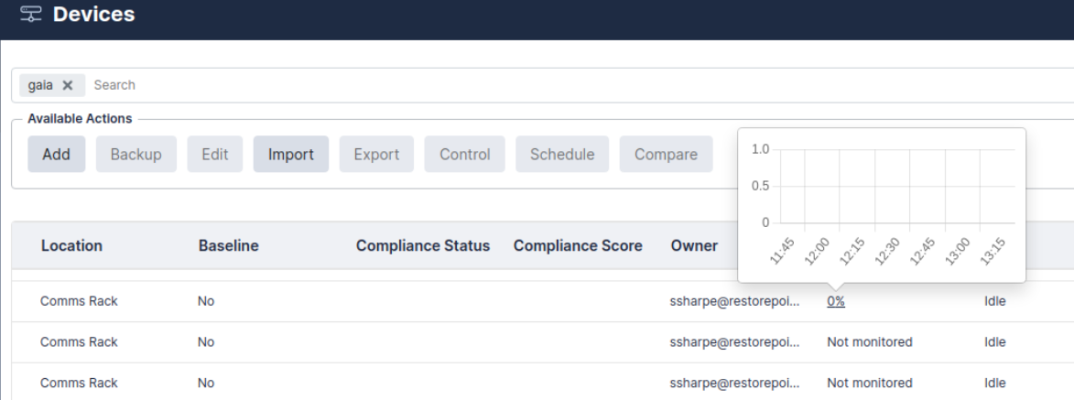
Tables display a grey header. For example, in the Device List page shown below, you can change column widths by double-clicking on the header, or by clicking and dragging the heading separators. You can change the sorting criterion by clicking on a column heading. You can also perform a full text search by typing in the Search field.
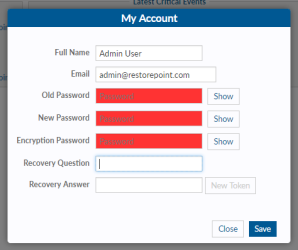
My Account
You can hover over the username on the top of the user interface for two options. The Logout option includes a clock that shows how many minutes until a user is automatically logged out, and the My Account option that allows you to change the following user settings:
-
Full Name
-
Email
-
Password
-
Encryption Password
-
Recovery Question
-
Recovery Answer
To change a password, you need to specify the Old Password.
For more information on the My Account options, see Adding a new user.
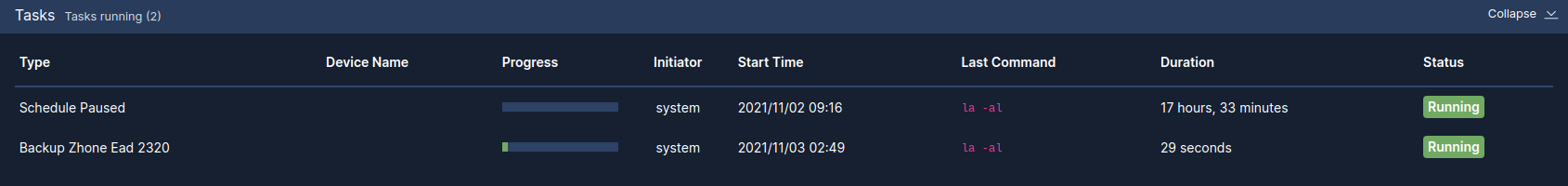
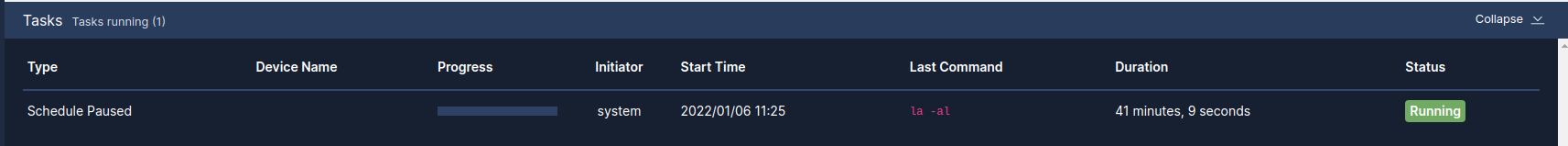
Activity Display
The Activity Display, shown below, displays a list of tasks that are currently running. This list is displayed on every page while tasks are in progress:
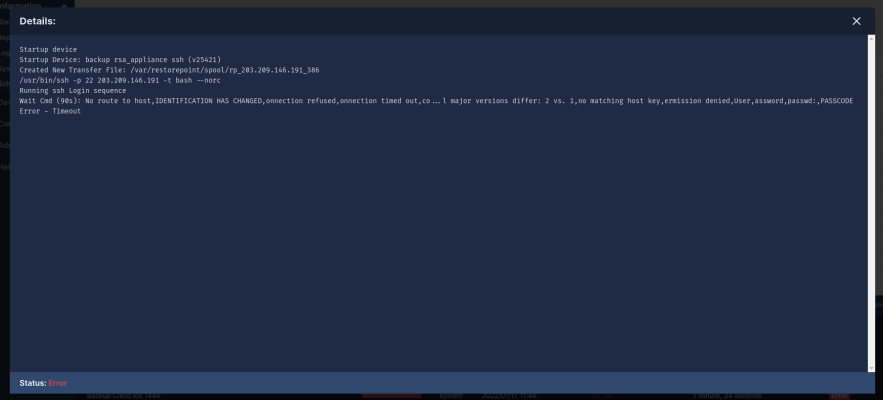
You can click on the magnifying glass icon to show the Progress Log, which displays real-time information about the running task:
Editing Views
In addition to the built-in views, every data table in Restorepoint can have multiple customized views. You can access these by clicking on the icon ( ) at the top left of the table. You can use this icon to reorder columns by clicking the up/down arrows and selecting the checkbox to show/hide columns.
) at the top left of the table. You can use this icon to reorder columns by clicking the up/down arrows and selecting the checkbox to show/hide columns.
You can define a name and save column orders, widths, and display settings using the Save button. You can delete saved views using the Delete button.
Views stored in your browser’s local storage are only available on the browser and workstation where they were set. If you clear your browser storage, you will clear any saved views.
Encryption
All sensitive data, including device configurations, stored in Restorepoint is protected by encryption. Restorepoint encrypts data when it is written to a disk and decrypts it as it is read. Cleartext data is only held in volatile memory. Therefore, the data disappears when the appliance is shut down or rebooted, rendering data theft impossible without a valid encryption key.
Restorepoint has two operational states:
|
Locked state |
When the appliance is powered up and no encryption password was entered by an administrator. In this state, Restorepoint cannot read its own database and therefore cannot perform any operations. An administrator must log in and provide the encryption password to unlock the database. |
|
Normal state |
Once an administrator provides the encryption password at login, all system functions are enabled. Subsequent administrator logins will not require an encryption password until the appliance is powered down or rebooted. |
The entire Restorepoint database is encrypted. Therefore, it is vital that administrators remember both their normal and encryption passwords. Administrators must also keep their emailed password-recovery tokens safe. For more information, see Connecting to Restorepoint After a Reboot and Password Reset.
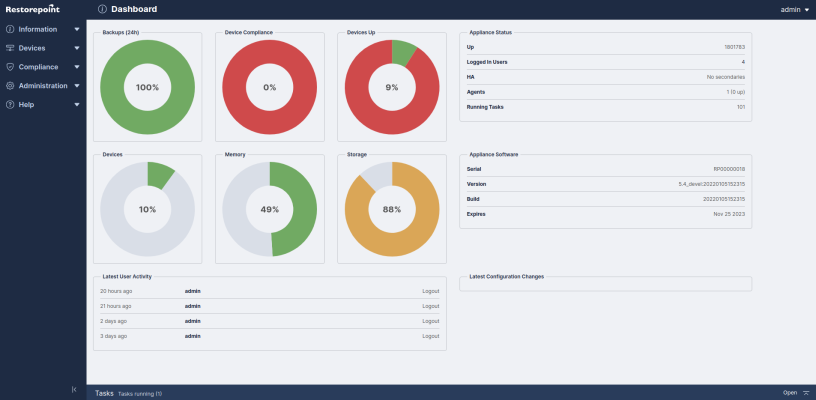
System Status Page
The System Status page or Dashboard, displays an overview of the health of Restorepoint and displays the number of devices being backed up. The following image is the default page when you first login to Restorepoint. You can display it at any time by clicking Info on the menu.
Graphs:
|
Backups (24h) |
The scheduled, successful, and failed backups in the last 24 hours. |
|
Device compliance |
The number of compliant and non-compliant devices, and the number of devices with no policy assigned. |
|
Device Baseline |
The number of devices that are running a baseline configuration, non-baseline configuration, and no baseline configuration set. For more information, see Configuration Baselines. |
|
Devices Up |
The number of devices that are currently being monitored and responding to Restorepoint. If you click on the graph, a moving average chart covering the past 24 hours is displayed. |
|
Storage |
The amount of disk space used and the total amount of disk space for the Restorepoint appliance. |
|
Devices |
The total number of devices configured on the appliance, and the maximum devices allowed on your current licence. |
|
Memory |
The amount of RAM currently being used by the Restorepoint appliance and the total amount of RAM available. |
|
Network Activity |
The current network activity, as seen by the Restorepoint appliance. |
|
Load Average |
The Load Average [https://en.wikipedia.org/wiki/Load_(computing) ] of the Restorepoint appliance, over the last 30s. |
Text panes:
|
Appliance Status |
The uptime, number of logged in users, High Availability status (if enabled), Agents status (if enabled), and number of running tasks. |
|
Appliance Software |
The serial number, version, build number (including a link to the change log for that version), and license expiration date of the Restorepoint installation. This information is also available in the footer. |
|
Latest user activity |
Administrator logins/logouts, and other user-initiated operations. |
|
Latest critical events |
Any backup failures, bad logins, or other important information. |
|
Latest Configuration Changes |
Any devices that have reported modified configurations. |
|
Activity display |
Appears on the left-hand side if any background processes are running. It also displays real-time task details and terminating a task details. |
Scheduled Tasks
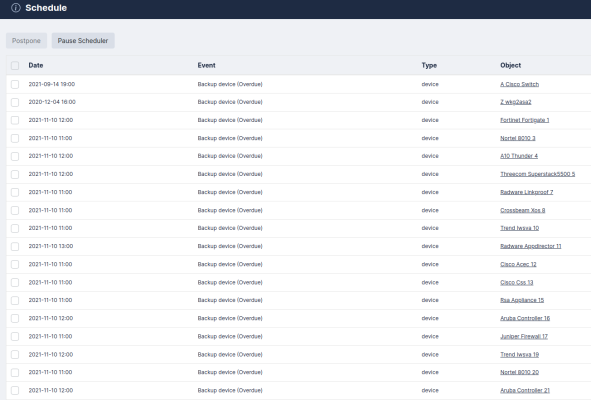
The Info > Schedule page displays the upcoming scheduled tasks, including the next backup for each of the devices configured in Restorepoint. Each item displays the following:
-
The date and time when the next task is due.
-
The task type (backup, discovery, archive, etc.).
-
The device, user, or system configuration object to which the task refers.
Any scheduled event can be postponed and remove the next occurrence of a scheduled task by selecting the relevant checkbox and clicking the Postpone button.
The entire schedule can be paused by clicking the Pause button. If you click the Pause button, no scheduled events will occur until the device is Unpaused.
Adding Devices to Restorepoint
You can add devices to Restorepoint using three methods:
-
Manually (For more information, see Manually Adding a New Device)
-
Importing a list from a CSV file (For more information, see Importing Multiple Devices Using a CSV File)
-
Using automatic discovery (For more information, see Device Discovery)
The Device List menu allows you to:
-
Display all the existing backups for a device
-
Compare the configurations of two devices
The Discovery menu allows you to:
-
Define the networks you wish to scan
-
Schedule a periodic network scan
-
Import discovered devices into the main device list
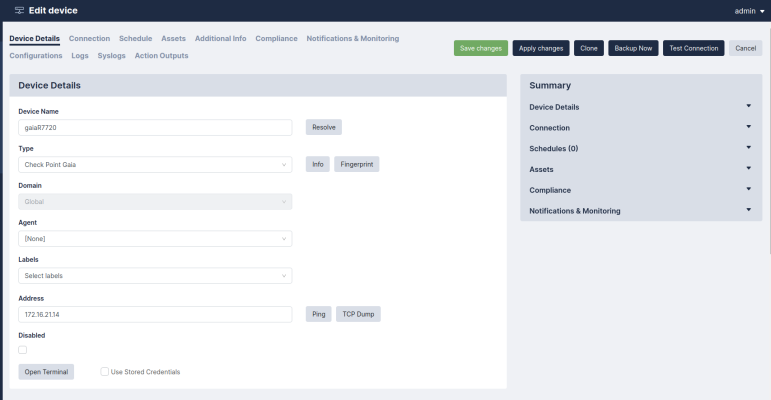
Manually Adding a New Device
How you configure a new device may vary slightly from one device to another. Please see device specific information in the Plugin Guide (Help > Plugin Guide).
To create a new device:
-
Navigate to the Device Management page (Devices > Device List).
-
Click the Add button on the top left hand corner of the page. The Add device page appears. Complete the following fields:
|
Device Name |
Enter a name for the device up to 64 characters long. If the name is defined in your DNS, you can click the Resolve button to automatically fill the IP Address field. Restorepoint will keep the IP address up to date with your DNS and manual changes to the IP address will be ignored. |
|
Type |
Select the device type. You can start typing in the Select plugin field to filter the list. This list only displays the device types that are currently available on your license. |
|
Domain |
Select the domain that the device is assigned to. This field is only present if Domain Administration is enabled on your appliance. For more information, see Administration Domains. |
|
Agent |
If the device is managed via an agent, select the appropriate agent from the dropdown list. |
|
Address |
Enter the IP address for the device. |
|
Open Terminal |
You can click this button to open a web-based virtual terminal to the device that you can use for troubleshooting. Selecting Restorepoint Credentials uses the credentials you have defined on the Connection tab, otherwise you will need to provide your own credentials for logging into the device. For more complex terminal use, ask your account manager about Restorepoint Universal Console. |
|
Owner Email |
Enter the email address of the device administrator. By default, this field is filled with the notification email address defined on the System Configuration page. |
|
Email on Config Change |
Select this checkbox to automatically trigger an email notification to the device owner when a device configuration change is detected. This option is not available for all device types. |
|
Email On Start Backup |
Select this checkbox to automatically trigger an email notification before a backup starts for this device. This notification creates a 1-minute delay before the backup starts. |
|
Email On End Backup |
Select this checkbox to automatically trigger an email notification when a backup completes. If this checkbox is not selected, Restorepoint will only send an email notification if the backup fails, or if a configuration change is detected and Email Config Change is selected. |
|
Syslog Change Detection |
If available on your Restorepoint system, select this checkbox for Restorepoint to automatically detect when a device is modified and automatically retrieve its configuration. Note that this feature is only available for specific devices. For more information, see the Plugin Guide (Help > Plugin Guide). |
|
Log Transcript |
Select this checkbox to create a full transcript log for this device for debugging purposes. A transcript log is automatically saved if the backup fails, so this is rarely needed. |
|
Types |
Select the types of configurations to backup for this device. |
|
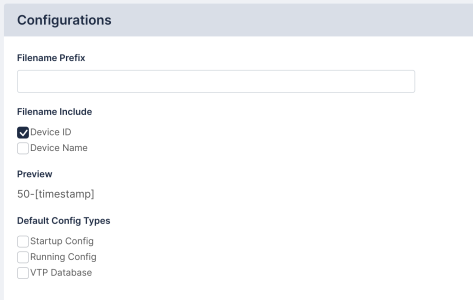
Filename Prefix |
Optionally enter a custom filename prefix for the device configuration files, and check the relevant fields to include. A preview of the filename will appear in the Preview field. |
|
Monitor |
Select this checkbox to monitor the device. For more information, see Device Monitoring. |
-
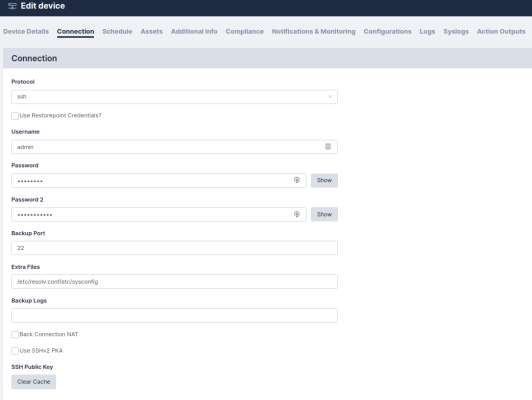
Select the Connection tab and complete the following fields:
|
Protocol |
Select the appropriate connection protocol for your device, such as telnet or SSH. The options may vary depending on the device type. |
|
Username |
Enter the administrator account username for the target system. |
|
Password |
Enter the password associated with the administrator account. For some devices you may need to enter more than one password. The field color ranges from red to green to indicate the password strength, according to the policy set in the Password Policies page. |
|
Use credentials |
You can select this checkbox and select a Credential Set instead of entering a username and password. Credential sets are reusable username/password combinations that can be shared among different devices (See Credential sets). |
|
Back-Connection NAT |
Select this checkbox if Restorepoint accesses this device through a NAT router or firewall. This option will only be displayed if the device requires back-connections and if Use NAT is selected in the System page. If a NAT IP Address is configured here, it will override the corresponding Domain (Section Administration Domains) and System (Section Network Address Translation (NAT)) settings. |
|
Use SSHv2 PKA |
Select this checkbox if you want to use SSH Public Key Authentication instead of password-based authentication when connecting to the device. Click the Show Keys button to display Restorepoint’s public SSH keys. |
|
Clear cache |
If you have replaced a device, Restorepoint may refuse to connect to it because it will detect that the device key has changed and display a connection error; this is a security feature of SSH. In order to override this feature, click the Clear Cache button. |
|
Backup Port |
If required for your device, enter the backup port you want to use. |
-
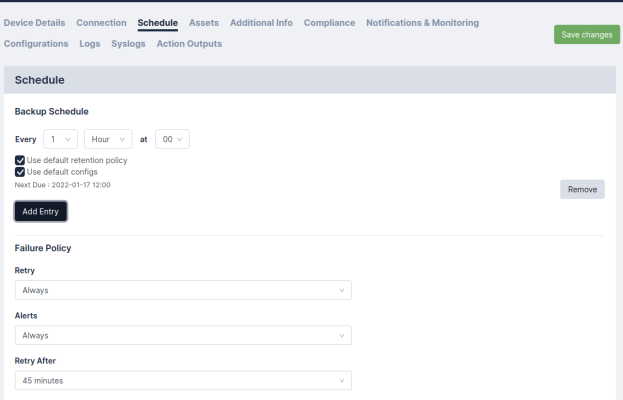
Select the Schedule tab (figure 3.10) to configure the backup schedule for the device, then click Add Entry to add one or more backup intervals.
For each schedule interval, you can override the config types to backup by selecting any of the Config Type checkboxes, or override the default retention policies by unselecting Use Default Policy. You can also override the Failure Policy on this page. For more information, see Backup failures.
-
Click the Assets tab to enter optional Asset Management details for the device.
By default, these include:
-
Asset ID
-
Firmware Version
-
History
-
Serial Number
-
Location
-
Notes
-
Manufacturer
-
Model
Custom fields can be added in the Custom Asset Fields page. For more information, see Asset Fields.
-
-
The Additional Info tab, if available, displays additional information retrieved from the device, such as license details, routing table, and network interfaces. You can also display the output of a saved Action on this page using the New Info Command dropdown. For more information on creating Actions, see Controlling a device.
-
Click the Compliance tab to assign compliance policies to this device. For more information, see Device Policies.
-
Click Save to finish creating the new device. The Device List page appears and the new device.
Select the device and click the Backup button to perform a manual backup, if required. The backup progress and completion will be shown in the Activity Display. If the backup is completed successfully, the indicator next to the device name is green, and the date of the last backup is added to the display.
Importing Multiple Devices Using a CSV File
If you need to add a large number of devices, you can click the Import button and select a comma-separated values (.CSV) file, that contains the device details.
When you create a comma-separated value (CSV) text file to import, include a line at the top of the file to indicate the columns for the attributes you want to import; the order is irrelevant. For example:
name,plugin,protocol,ip_address,username,password,password2,backup_port,keep_backup,owner,serial_no,asset_id,location,notes
where:
|
name |
The device name (required field) |
|
plugin |
The device type, e.g. ‘Cisco ASA’ or ‘cisco_asa’ |
|
protocol |
The connection protocol, e.g. ‘telnet’ or ‘ssh’ (required field) |
|
ip_address |
The device IP address |
|
username, password, password2 |
The login credentials for the device |
|
backup_port |
The port to use to connect to the device, if required |
|
keep_backup |
The backup retention policy (days) |
|
owner, serial_no, asset_id, location, notes |
Optional fields |
Device Discovery
The Restorepoint device discovery engine uses a variety of methods to discover hosts on your network that can be imported to the main device list. You can also be notified by email of new devices that are installed on your network.
Device discovery is not guaranteed to discover all the relevant devices on your network. Firewalls or the device configuration itself may negatively affect the discovery process. Similarly, the device type may not always be detected correctly. When you import a device, you are able to override the detected type.
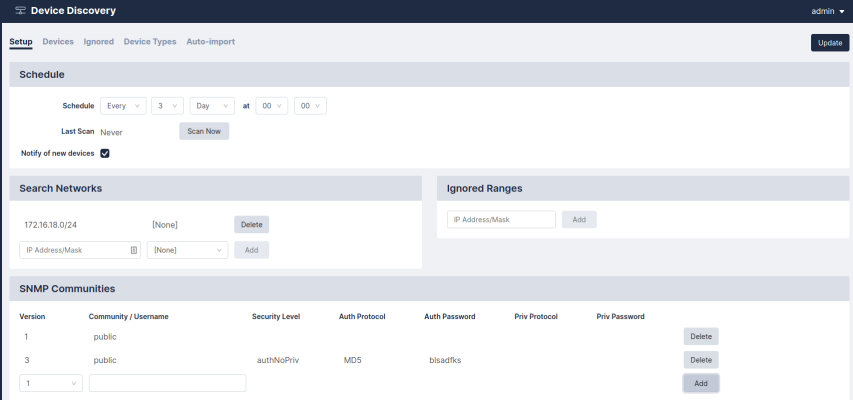
Discovery Setup
To configure discovery, follow these steps:
-
Select Discovery from the Devices menu. The discovery setup page appears.
-
Add one or more network ranges (in CIDR notation) to scan on the Search Networks list, for example:
10.20.0.0/16. -
If you do not wish to scan a particular range, for example
10.20.10.0/24, add this to the Ignored Ranges list. -
You can optionally add one or more SNMP communities in use on your network: choose the SNMP version, enter a community string, and then click the Add button.
-
If you want to be notified of a new device, select the Notify of New Devices checkbox.
-
If you want to use the Cisco Discovery protocol (https://en.wikipedia.org/wiki/Cisco_Discovery_Protocol), select the Use CDP checkbox.
-
If you want to use the Link Layer Discovery protocol (https://en.wikipedia.org/wiki/Link_Layer_Discovery_Protocol), select the Use LLDP checkbox.
-
Choose a scan schedule.
-
Click Update to save your changes.
-
Click Scan Now to start the scan.
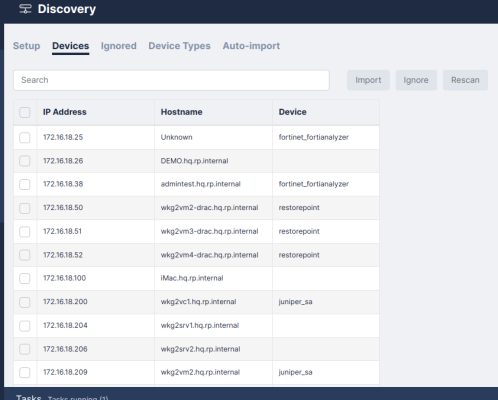
Discovered Devices
At the end of a discovery scan, a list of discovered devices is displayed:
Select one or more devices, then click Import to import them to the main device list. If only one device was selected, the New device page appears with all the discovered information automatically populated. After you review all of the information and make any necessary changes, click Save to import the device. If multiple devices are selected, they will be imported without preview. The devices are marked as incomplete and displayed in red in the device list. You can then complete the configuration by adding authentication details or by modifying any default parameters.
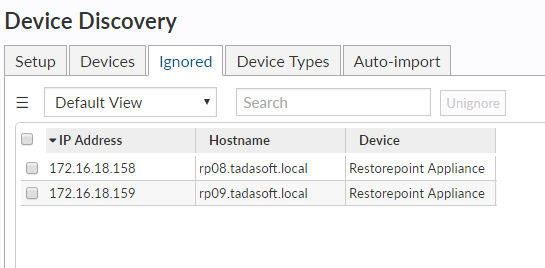
Ignored Devices
The Ignored devices screen displays a list of devices that will be ignored in future scans. To remove devices from the ignore list, select the devices then click Un-ignore.
Device Types
The Device Type Override screen allows you to force discovery scans to import a device as a certain type based on a hostname pattern.
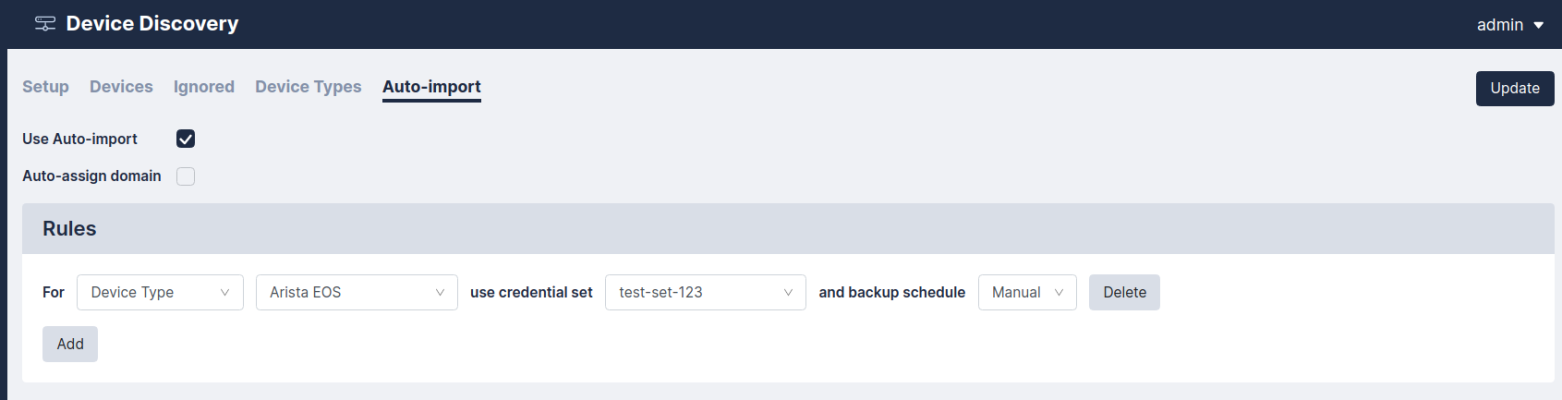
Automatic Import
Select the Use Auto-Import checkbox to automatically import discovered devices into the device list.
If you are using Domains, select the Auto-assign Domain checkbox to automatically add a discovered device to a domain based on its IP address.
Next, add one or more auto-import rules. Rules determine the credentials and backup schedule that are used for imported devices. The rules can be determined by detected device type, hostname, IP address range, or detected location.
Running a Manual Backup
To run a manual backup:
-
Select Devices from the menu. The Device List page appears.
-
Select the devices you want to back up and click Backup Now.
You can also run a manual backup by clicking the Backup Now button on the Edit Device page.
Scheduling an Automatic Backup
To automatically schedule backups for a large group of devices by spreading the backups over a day, a week, or a month. To automatically schedule backups, select the relevant devices on the Devices screen, and click the Schedule button. Select the desired time interval, and the daily Start/End time and/or the Start/End day. For example, you to run backups only at night, or during the weekend.
Exporting the Device List
Click the Export button to save the device database in a CSV file.
Editing an Existing Device
To edit an existing device:
-
Click on the relevant device name. The Edit Device page appears.
-
Make any required changes and click the Save button.
Editing Multiple Devices
You can apply values for multiple devices at once by selecting the devices and clicking Edit. The Edit Device screen displays [Multiple] for all values that are not common to the selected devices. You can change a value for all the devices by editing the field and clicking Update.
You can use this feature in addition to device grouping - for instance, all Cisco devices may be set to back up hourly by Grouping by Manufacturer, selecting the Cisco group checkbox to select all Cisco devices, selecting Hourly, and clicking Update.
Deleting an Existing Device
To delete an existing device:
-
Select the device(s) you want to remove.
-
Click Edit, and ensure that the Disabled field is set to Yes to prevent accidentally deleting a device you have not disabled.
-
Click Save.
-
The devices you want to remove are selected. Click Delete.
Device Monitoring
Restorepoint can monitor devices by periodically checking that the TCP port used for backup (for example, telnet or SSH) is accepting connections, or by sending ICMP Echo Requests (pings) to the device. Monitoring is disabled by default and can be enabled or disabled for each individual device.
Enabling Monitoring
To enable monitoring, open the relevant device Edit screen:
-
Select the Monitor Device checkbox
-
Select the Type of monitoring required. Normally, the device’s TCP port used for backup is polled; if the Ping option is selected, the ICMP Echo Request (ping) will be used.
-
You can select Email when down to send an email notification if the device appears to be down. You can also choose to receive Email when up.
-
If the device fails to respond after the number of attempts specified in the Fail after box, it is considered “down”.
Displaying Monitoring Information
You can hover over status information to display a Round Trip Time graph between Restorepoint and the device, in 5 minute intervals.
Clicking Uptime will display the monitoring graph for the device.
You can select any other monitored device from the dropdown at the top of the page to display its graphs.
Configuration Templates
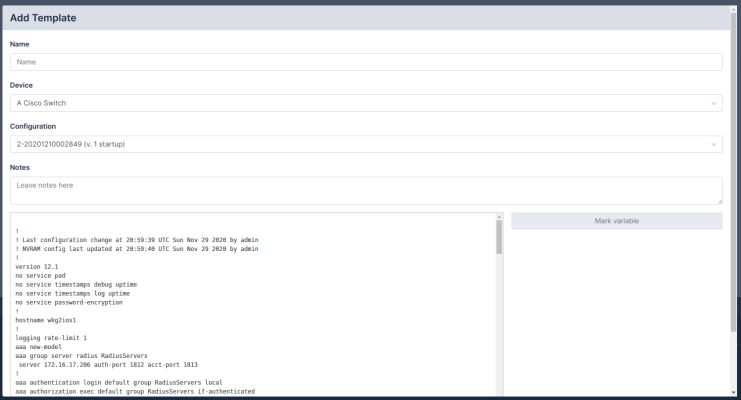
Templates are configurations that can be pushed to multiple devices. For example, during a large deployment of similarly configured devices. Each template can contain parameters, which are substituted for entered values for each device. For example, a section may be marked “IP Address”, and the field will be applied when pushed to devices.
Creating and Editing Templates
-
Navigate to the Template page (Devices > Templates). Click Add, or click on an existing template name.
-
For new templates, select a device and configuration to base the template on.
-
After your template has loaded, select the configuration fields that you want to be substituted.
-
Click Mark Variable to name and store a highlighted value.
-
Once your template is created, the template values can be renamed or deleted with the relevant buttons.
-
Click OK. If you don’t provide a name and comment, a name and comment will be automatically generated.
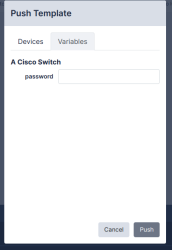
Pushing Templates
To push a template to a device, select the template from the Template Management page. Choose one or more devices using the device selector, and click Push.
If the template has any parameters, you must enter the values for each of the devices selected above:
Click OK to complete the operation.
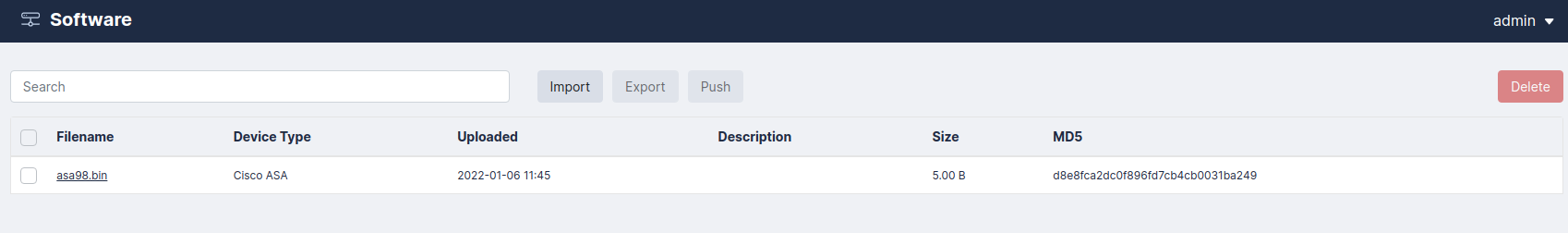
Software Management
Restorepoint can be used as a repository for device firmware/software that allows you to upload files like firmware images and ISO images to the appliance. Software images can also be pushed to supported devices.
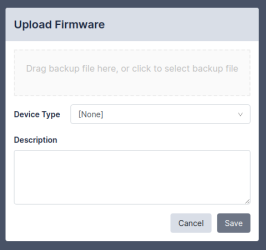
Uploading and Editing Firmware Images
-
Click Import, or an existing firmware name.
-
For new firmware, click the Browse button and navigate to the file from your hard drive.
-
Supply values in the Device Type and Description fields.
-
Click Save.
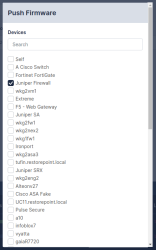
Pushing Firmware
Restorepoint can upgrade the firmware of a supported device using an image stored in the repository. Select a firmware image using the tickboxes, then click Push. Select the device from the menu, then click Push again; Restorepoint will perform the upgrade procedure recommended by the device vendor.
Please check the Plugin Guide (Help > Plugin Guide) for a list of devices that support this function.
Credential Sets
Restorepoint can use predefined Credential Sets to authenticate to a device instead of individual usernames and passwords. Credential Sets are useful if several devices share the same authentication credentials. To create a Credential Set:
-
Select Credential Sets from the Devices menu.
-
Click Add Set, or click on an existing Credential Set name.
-
Give the Set a name, then fill in the authentication details .
-
Select a Domain from the pull-down menu to restrict the scope of this set to a particular domain; otherwise choose Global to make this set available to all domains.
-
Click OK.
Using Credential Sets
To authenticate to a device using an existing credential set, leave the authentication details empty, check Use Credentials, and then select the correct credential set. Click Save.
To see what devices are currently using a given Credential set, click the name on the Devices > Credential Sets page, and navigate to the Devices tab.
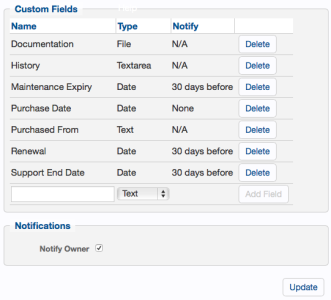
Asset Fields
In addition to the built-in Asset Management fields, you can also define custom fields. To do this, navigate to the Assets Fields page (Devices > Asset Fields). Custom fields can be of type Date, Text (single-line), Textarea (multiple-line), and File.
Once defined, date fields can be set to give an Expiry Notification:
-
60 days before
-
30 days before
-
When Reached
If set, an email is automatically sent to the device’s owner on the specified expiration date. Expiry date is also used in reports.
Any custom fields defined in this page become immediately available in the Assets page of all devices managed by Restorepoint.
Global Search
Restorepoint can search the full text of configuration backups for a keyword from the Global Search page (Devices > Global Search).
Enter your search term in the Search for box, select the devices you would like to search, and click Go. To avoid excessive results, you can choose to Limit the search to a given timeframe.
If the keyword (or keywords, if more than one is entered) are found in a device configuration, it will be listed in the right-hand panel. If you click the name of the device configuration, the device configuration page will open.
Global searches are case-insensitive and do not support wildcards.
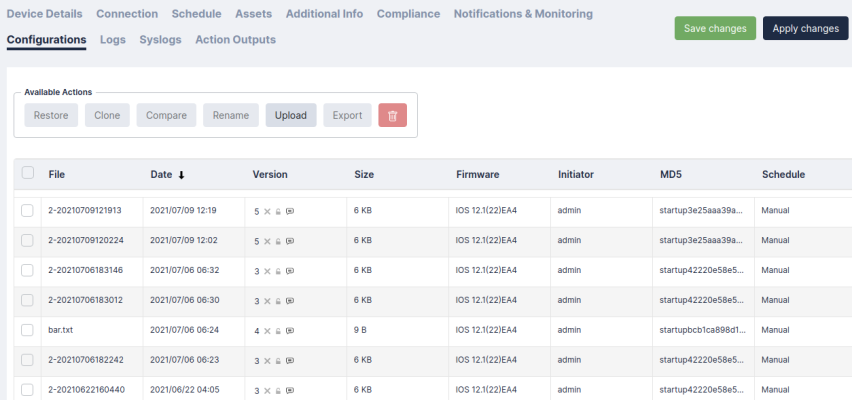
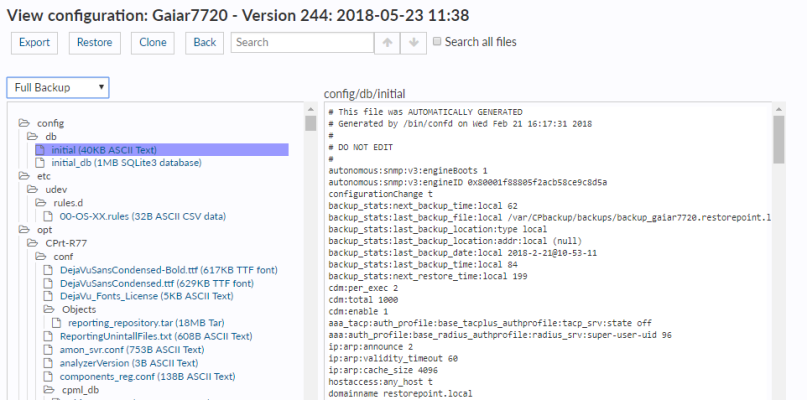
Viewing the List of Configurations for a Device
You can access the list of configurations for a device from the Device Management page by clicking the last backup column of the corresponding device, or by clicking the Configurations tab when you edit the device.
A configuration may contain more than one file. For example, a Cisco IOS device has a start-up and a running configuration; you can choose which configurations should be backed up in the Device Details page.
If a device supports firmware identification, Restorepoint will display the firmware version detected at the time of backup, next to each configuration. A sample list is shown below:
Restorepoint keeps track of configuration changes by assigning a version ID to each unique configuration retrieved from a device. Identical configurations are not stored multiple times.
|
View |
|
|
Baseline version |
The checkmark shows the baseline version of a configuration. To set a baseline version, select the checkmark. The checkmark will become solid. Restoring a non-baseline configuration version to a device with a baseline configuration version will cause a compliance alert. For more information, see Configuration Baselines. |
|
Retaining a version |
You may want to retain a configuration indefinitely (a milestone configuration), that overrides your configured retention policy. For example, a backup taken just before a device upgrade. To retain a configuration, click the padlock icon next to the file name; the padlock will become solid. To undo this action, click the padlock icon again. |
|
Adding comments |
You can add a comment to a configuration by clicking the grey note icon next to the relevant configuration. Enter your comment in the pop-up dialog box and click OK; the icon will change color . To remove a comment, click the icon , delete the text, and click OK. |
the above options apply to a configuration version, rather than an individual backup.
|
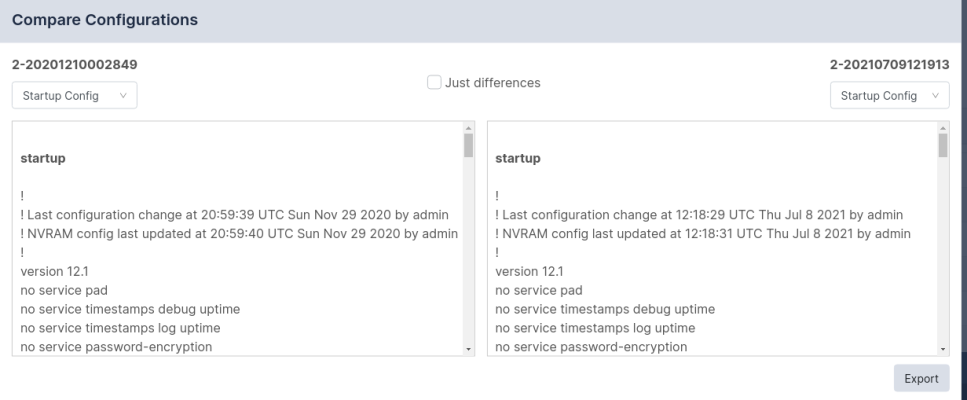
Compare configurations |
The Compare option is only available for the devices with text file or a tar/tgz archive of text files configurations. To compare two configurations, select two items using the checkbox to the left of the item, and click Compare. If the configurations are archives, Restorepoint will expand the archives and compare the individual files. Restorepoint will display the chosen configuration files side by side and highlight the differences; inserted lines will be displayed in blue and changed lines will be displayed in red. When Only differences is selected, Restorepoint will not display lines which are identical in both files, except those preceding or following a change. Note: Some devices embed a timestamp or fingerprint in the configuration every time a backup is performed. Wherever possible, Restorepoint ignores lines that only differ by such fingerprints when comparing configurations, so that only relevant changes are displayed. |
|
Delete a configuration |
Select a configuration using the checkbox and click Delete. This operation is usually only required to delete a milestone configuration (one you have chosen to retain indefinitely), because old configurations are automatically removed according to the retention policy. |
|
Restore a configuration |
To restore a configuration, select a configuration using the checkbox and click Restore. Additional options may be displayed, for instance which configuration type should be restored, or whether the device should be reset to complete the operation. |
|
Upload Backup |
This option allows you to upload a new device configuration file to Restorepoint from your PC. |
|
Export Backup |
You can export a device configuration from Restorepoint through your browser, email, make it available for FTP/TFTP/SFTP collection by a device, or export it to one of your pre-configured file servers. |
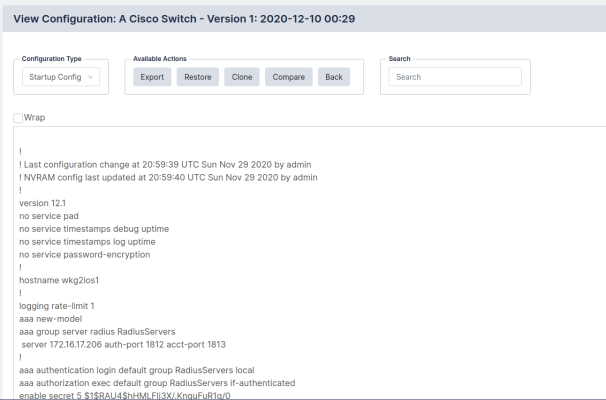
Backup File Operations
If a device configuration is a plain text file or a tar/tgz archive of text files, you can view the configuration contents by clicking the relevant tab or file name in the configuration page. If the configuration is an archive of text files, Restorepoint will attempt to unpack the archive and display each individual file. If the configuration is a binary file, or if the file is too large, Restorepoint will not display the contents.
From this page, you can copy this file to your local machine by clicking the Export button. After you export the file, you can use a text editor to edit the backup file, and then upload it back to Restorepoint using the Upload Backup button on the Configurations tab. You can push the edited configuration file to the device by clicking the Restore button.
Backup Failures
By default, after a device fails to back up, Restorepoint will retry the operation every hour until it succeeds, and it will send an error notification by email on every failed attempt. This behaviour can be modified by changing the Failure Policy, configured in the device Schedule tab:
-
From the Retry pull-down, choose how many times to retry a failed backup. Backups are attempted every hour.
-
Next, choose whether to revert to the set schedule or disable further backups when the last allowed failure occurs.
-
Finally, choose when to be notified of a failure.
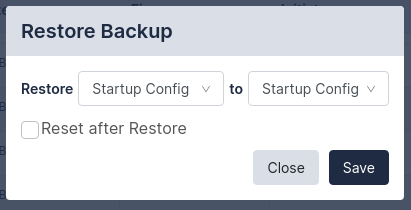
Restoring to an Existing Device
To restore a device:
-
Select Devices from the menu. Restorepoint displays the Device Management page.
-
Click the entry in the Last Backup column next to the device you want to restore. Restorepoint displays all the available configurations.
-
Select a configuration by selecting its checkbox and click Restore. Restorepoint prompts you to confirm the restore operation. Depending on the device type, you may be prompted for additional options.
-
If the restore operation fails, you will see an activity in the activity display. You can click on the magnifying glass icon next to the progress bar to show a real-time progress log, which will aid in determining the cause of the failure. There is also a Transcript in the Logs tab for failed backups, which contains the details of the conversation with the device.
Restoring to a New Device
When a device is replaced, for instance due to failure, the following conditions must be met:
-
The new device must run the same software version as the original.
-
The new device must be configured with the same IP address and authentication details as the old device. Alternatively, you can temporarily change the IP addresses or credentials stored on Restorepoint to match those of the new device.
-
If Restorepoint connects to the device using SSH, you may to need clear the SSH cache in Restorepoint in the Connection tab of Device Management.
Cloning
The Clone button restores a configuration to a device that is different than the original, which produces a duplicate of the original device. This operation should be used with caution, as it may produce a duplicate IP address on your network.